 Miscellaneous
Miscellaneous  Miscellaneous
Miscellaneous  Politics
Politics 10 Lesser-Known Far-Right Groups of the 21st Century
 History
History Ten Revealing Facts about Daily Domestic Life in the Old West
 Weird Stuff
Weird Stuff 10 Everyday Products Surprisingly Made by Inmates
 Movies and TV
Movies and TV 10 Actors Dragged out of Retirement for One Key Role
 Creepy
Creepy 10 Lesser-Known Shapeshifter Legends from Around the World
 Animals
Animals 10 Amazing Animal Tales from the Ancient World
 Gaming
Gaming 10 Game Characters Everyone Hated Playing
 Books
Books 10 Famous Writers Who Were Hypocritical
 Humans
Humans 10 of the World’s Toughest Puzzles Solved in Record Time
 Miscellaneous
Miscellaneous 10 Ironic News Stories Straight out of an Alanis Morissette Song
 Politics
Politics 10 Lesser-Known Far-Right Groups of the 21st Century
 History
History Ten Revealing Facts about Daily Domestic Life in the Old West
Who's Behind Listverse?

Jamie Frater
Head Editor
Jamie founded Listverse due to an insatiable desire to share fascinating, obscure, and bizarre facts. He has been a guest speaker on numerous national radio and television stations and is a five time published author.
More About Us Weird Stuff
Weird Stuff 10 Everyday Products Surprisingly Made by Inmates
 Movies and TV
Movies and TV 10 Actors Dragged out of Retirement for One Key Role
 Creepy
Creepy 10 Lesser-Known Shapeshifter Legends from Around the World
 Animals
Animals 10 Amazing Animal Tales from the Ancient World
 Gaming
Gaming 10 Game Characters Everyone Hated Playing
 Books
Books 10 Famous Writers Who Were Hypocritical
 Humans
Humans 10 of the World’s Toughest Puzzles Solved in Record Time
10 Underhanded Ways Governments Use The Modern Media
The Internet has effectively ended the era of government monopoly on information. There are countless examples of citizens successfully using social media and smartphones to self-organize and challenge authoritarian governments.
So what do you do if you’re a ruler threatened by these developments? Sure, you could settle for old-school methods of exerting control: limiting Internet access, censoring information, or replacing all public billboards with giant portraits of yourself.
Or . . . you could embrace these modern means of communication and use them to your advantage.
10Russia Edits Wiki Entries Related To MH17

In the wake of the MH17 tragedy in 2014, questions of who’s responsible for downing the plane emerged almost immediately. Eventually, a growing body of evidence pinned the blame on the pro-Russian forces, who’d likely shot down the plane with a Buk anti-aircraft missile system brought in from Russia. In parallel, Russian media outlets began to spin numerous conspiracy theories about the event, ranging from the idea that MH17 was actually the lost MH370 to the plane having been loaded with already-dead bodies prior to departure.
But it seems that someone in the Russian government decided to get involved in a much more direct way—by editing Wikipedia articles related to the event. The day after MH17 went down, a section of the Russian Wikipedia article about the incident was changed to directly implicate the Ukrainian military. A passage was changed to read: “The plane was shot down by Ukrainian soldiers.” Luckily, there’s a Twitter bot established specifically to track Wikipedia edits made from Russian government IPs. This bot flagged the attempted change, and Russia learned a valuable lesson about trying to manipulate crowdsourced information.
That lesson was promptly forgotten when, just a few days later, another Wikipedia article was edited in a similar manner. By then, the Russian Ministry of Defense had floated its own explanation of the event. According to that theory, MH17 was shot down at an altitude of 10,000 meters (33,000 ft) by a Ukrainian Su-25 jet. The problem with that theory? The Su-25 has a service ceiling of only 7,000 meters (23,000 ft)—and that’s without the ordnance. So, to give credence to the claim, Russia took to Wikipedia once again and “corrected” the plane’s service ceiling to 10,000 meters (33,000 ft).
The above edits are just a drop in a much larger bucket. Russian state agencies are responsible for as many as 7,000 similar updates to Wikipedia over the course of 10 years.
9China’s ‘50-Cent Party’

Let’s move past the obvious Curtis Jackson jokes and straight to China’s paid social media commentators. Hired by the Chinese government, these freelancers get 50 Chinese cents for each post they make on online forums. What kind of posts are we talking about? In a nutshell, anything that helps steer public opinion in the direction desired by the government.
These paid opinion makers receive email instructions about what topics to focus on, where to steer the conversation, and, occasionally, what specific websites to visit. The work itself can get pretty schizophrenic, since 50-centers usually find themselves playing different roles and even arguing with themselves using multiple fake accounts. They also have to maintain a careful balance between shaping the discussion and not appearing so obviously official as to risk being called out.
In 2014, the 50-Cent Party were suspected to be behind a Twitter campaign that presented an overly positive version of people’s lives in Tibet. Twitter profiles of handsome foreigners shared links to videos and articles extolling Tibetans’ perfect life under Chinese rule. The catch? These Twitter accounts were fake. Their profile pictures were photos of celebrities, and they linked almost exclusively to Chinese propaganda sites. While the connection between these profiles and the 50-Cent Party was never definitively established, observers like Alistair Currie of Free Tibet name these hired lurkers as the most likely culprits.
8Yanukovych Government Sends Threatening Texts To Protesters

In late January 2014, Ukraine’s president Viktor Yanukovych was facing increasingly violent opposition to his rule. What began in November 2013 as a peaceful demonstration against his decision to back out of an association agreement with the European Union had soon turned into progressively brutal clashes between the protesters and riot police.
On January 16, in a misguided attempt to control the situation, Yanukovych enacted anti-protest laws that limited freedom of speech and assembly. The media and protesters dubbed them “dictatorship laws,” and people took to the streets in defiance. When they did, they received the following message on their cell phones: “Dear subscriber, you are registered as a participant in a mass riot.”
Yanukovych—having learned little from how Ukrainians reacted to him slowly turning despotic—decided to up the ante by trying to intimidate the protesters into submission. According to three mobile network operators, the government used a “pirate” cell phone tower to push the messages out to their subscribers, turning the very phones they used to coordinate the protests into tools of psychological pressure.
Unfortunately for Yanukovych, and tragically for the rest of Ukraine, these attempts at playing tough escalated into a bloody showdown between government forces and the protesters in late February. The fights left as many as 100 people dead and over 500 wounded, ultimately leading to Yanukovych fleeing the country.
7US Military’s ‘Persona Management’ Program

Not content with simply spying on your mundane Facebook updates under the Prism program, the US has apparently also dabbled in a bit of online manipulation.
In 2011, it was revealed that the US military was working on a “persona management program,” which would allow them to shape online conversations. By using special software, each US operator could control up to 10 sock puppets—fake online identities with rich histories and backgrounds. These personas could then publish blog posts and leave comments in chat rooms and online forums. The main idea was to use these fake identities to infiltrate foreign-language extremist organizations and counter enemy propaganda.
A spokesman for United States Central Command said this technology would not be used on English-language forums or to address US audiences because of legal issues. Using fake identities, it would seem, is only legal when foreign audiences are involved. As such, interventions would happen in Arabic, Farsi, Urdu, and Pashto. The $2.6-million contract for the program was awarded to a cyber-security company called Ntrepid, which has so far been unavailable for comment.
Not much recent information is available about the fate of this program, but if you plan on browsing any Arabic chat rooms, we’d recommend keeping your comments on the up-and-up—just in case.
6ISIS And ‘The Dawn Of Glad Tidings’
In addition to being ruthless murderers, ISIS leaders have proven themselves to be surprisingly good at promoting their cause on social media. They produce impressive propaganda videos, maintain live picture feeds, and engage with their many Twitter followers through creative hashtag campaigns.
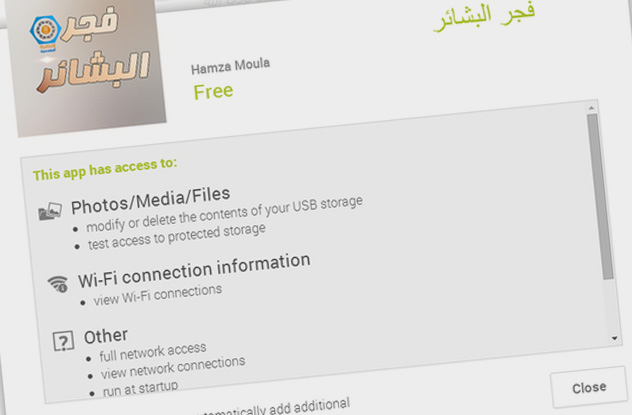
Speaking of Twitter, did you know that ISIS had its very own Twitter app for Android phones? Because it did. Google allegedly removed the app shortly after its launch, but for a while in 2014, anyone could head on over to the Google Play Store and download their very own ISIS app. The app was called “The Dawn of Glad Tidings” (or simply “Dawn”) and was promoted as a way to keep abreast of all ISIS developments. Once you downloaded Dawn, it would request access to a good deal of your account details.
So what happened to those who were okay with an evil militant group gaining access to their personal information? Dawn would turn its host phone into a sort of Twitter zombie, making it post random tweets on the user’s behalf. The content of those tweets was determined by ISIS operatives and would usually accompany an offensive operation by the group. At one point, the app posted as many as 40,000 tweets in a single day. You can say what you want about ISIS fighters, but you can’t accuse them of neglecting a marketing opportunity.
5Israel Pays Students For Pro-Government Messages On Social Media

In August 2013, Israeli Prime Minister Benjamin Netanyahu’s office announced an upcoming initiative to get the country’s students involved in generating pro-Israel messages on social media. The deal was pretty straightforward: The government would offer students university scholarships. In return, these students were expected to advance the country’s viewpoints online. One Israeli official referred to this as “putting public diplomacy in the hands of the public.”
At the outset, there was a bit of controversy surrounding the initiative. Israeli daily paper Haaretz claimed that the man heading these government efforts was Danny Seaman, a public diplomacy official. However, there was a minor problem with Seaman: He had a tendency to post rather bigoted anti-Muslim posts on his Facebook page. He was hardly the man you’d want behind a program that specifically aims to put a positive spin on Israeli government. Seaman was instructed by Netanyahu’s office to “immediately cease from making such pronouncements,” and his inflammatory statements were soon erased.
In 2014, a group of 400 students launched an “Israel Under Fire” project. Their aim was to promote the Israeli side of the picture in the bloody Gaza conflict and to counter what they perceived as Hamas propaganda. They were all volunteers and didn’t mention receiving any scholarships, but what they did was very similar to the initiative described above. The students had people translating Hebrew messages into 30 languages, a graphics team working on shareable charts and images, and even a video-editing department. Despite their volunteer status, the students did get official endorsement from the government, which even paid to promote some of their posts on Twitter. Unsurprisingly, their work had some critics, who believed it ran the risk of simply becoming government propaganda masquerading as authentic public discourse.
4Saudi Arabia Suspected Of Using Spyware
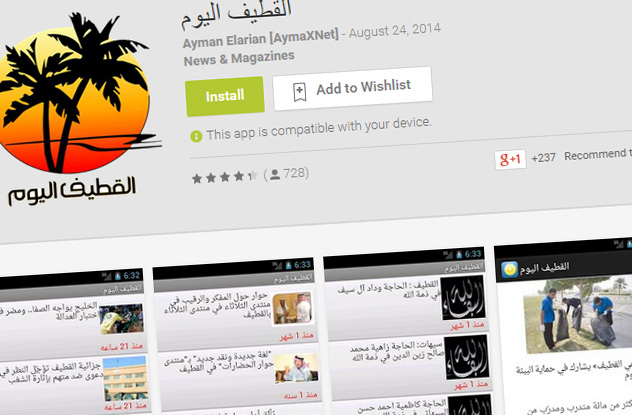
According to Human Rights Watch, Saudi Arabia’s government may be infecting the smartphones of its citizens with a malicious app. Disguised as a legitimate Android news app called “Qatif Today,” this imposter app gives its creators access to a wealth of information about the smartphone user. This includes any stored emails, text messages, contacts, call history, and even files from social media apps and popular mobile applications like Viber and WhatsApp. As if that wasn’t enough, it also allows a remote operator to control the phone’s camera and microphone to take pictures and record conversations, taking surveillance of citizens to a whole new, disturbing level.
The spyware contained in the app has been developed by an Italian firm called Hacking Team. The spyware is supposed to be used for criminal investigations and gathering intelligence for counterterrorism purposes. However, its use becomes more problematic in a country where any form of dissent and civil protest can be seen as terrorism, which is why Human Rights Watch is raising a red flag. Saudi Arabia isn’t the only country whose government is under scrutiny for using the spyware. Human Rights Watch has previously documented similar usage of the software by the Ethiopian government to spy on journalists and opposition leaders.
3Britain’s 77th Brigade

Not to be outdone by its US counterpart, the British Army is launching an online initiative of its own. Expected to start work in April 2015, 1,500 members of the newly created 77th Brigade will be responsible for “controlling the narrative” in all major interactive media.
It appears that the 77th Brigade won’t be hiding behind any fake identities though. Instead, these soldiers—recruited from the British Army and Territorial Army reservists—will disseminate information via Facebook, Twitter, smartphones, and other media to counteract perceived threats from aggressive disinformation campaigns. They already have a nickname: “Chindits,” named after British commandos serving in Burma during World War II. The 1,500 Chindits are required to have journalism experience and social media skills.
The formation of the 77th Brigade is seen partially as a response to successful recruitment and disinformation campaigns by ISIS and Russia, respectively. The Chindits expect to focus on building trust and sharing information, and they generally seem to have a more innocuous objective than most other examples we described. Well, as innocuous as something labeled “non-lethal warfare” and “psychological operations” can be.
2China’s Smartphone App That Spies On Protesters

Hong Kong’s pro-democracy protesters appear to have no intention of abandoning their cause and are taking to the streets once again. The Occupy Central (With Love And Peace) movement started in late 2014 as a response to China’s decision to reform the electoral system in Hong Kong. Under this new reform, Hong Kong voters would no longer be able to endorse their own candidates for Legislative Council. Instead, a special committee would first propose a few candidates to be voted on by the general public.
The protesters, who are demanding a return to the original voting setup, have successfully used social media and smartphones to organize their activities. Seemingly taking cue from Saudi Arabia, the Chinese government has allegedly used a smartphone app to spy on the protesters. To add insult to injury, the app pretended to have been developed by Occupy Central protesters themselves. Protesters would receive WhatsApp messages that read: “Check out this Android app designed by Code4HK for the coordination of Occupy Central!” Once downloaded, the app acts in a manner very similar to the one developed by Hacking Team. It gains access to the owner’s phone book, browsing history, location, and so on. And yes, it can also record audio.
A US firm called Lacoon Mobile Security flagged the app as a potential issue. According to them, the app uses such sophisticated software that it “is undoubtedly being backed by a nation state.” However, the Chinese government has denied any cyber spying on its part.
1The Kremlin Troll Army

Much like China’s 50-Cent Party, Kremlin’s trolls take to the Internet to influence opinion. Unlike their Chinese colleagues, however, Russian trolls are full-time employees and are part of an extremely well-organized operation. Multiple office buildings around Russia are staffed almost exclusively with these paid, pro-Kremlin commenters.
The most famous of these “troll farms” is located in the village of Olgino, close to St. Petersburg. That’s why the pro-Kremlin commenters are often called “Olgintsy.” They tend to have very targeted job assignments, usually focusing on specific blogs or opposition figures. They’re expected to post a specified number of comments per day, maintain numerous social media accounts, and even have subscriber and follower targets.
It was a 2013 investigation by local Russian reporters that first put Olgino on the map. Reporters uncovered an aggressive anti-opposition and anti-Western operation. Opposition leaders were compared to Hitler, and the US was called Russia’s “worst enemy.” Since then, this trolling enterprise has only been ramped up further, reaching a budget of $10 million in 2014. Some websites covering the Russia-Ukraine conflict, like The Guardian, appear to have been particularly badly hit, their comments section rendered effectively meaningless by an avalanche of pro-Kremlin posts.
Just how much of an impact the Kremlin campaign has is debatable. But some of those who document Russia’s disinformation, like Catherine Fitzpatrick, believe that these trolls succeed in crowding out legitimate commenters by forcing them to self-censor: “You don’t participate. It’s a way of just driving discussion away completely. Those kinds of tactics are meant to stop democratic debate, and they work.”
Daniel edits words for Listverse, writes words for Cracked, and does other stuff on his humor blog.








